Here is my Offical Version (Virus Sourcecode from packed Executable is attached!):
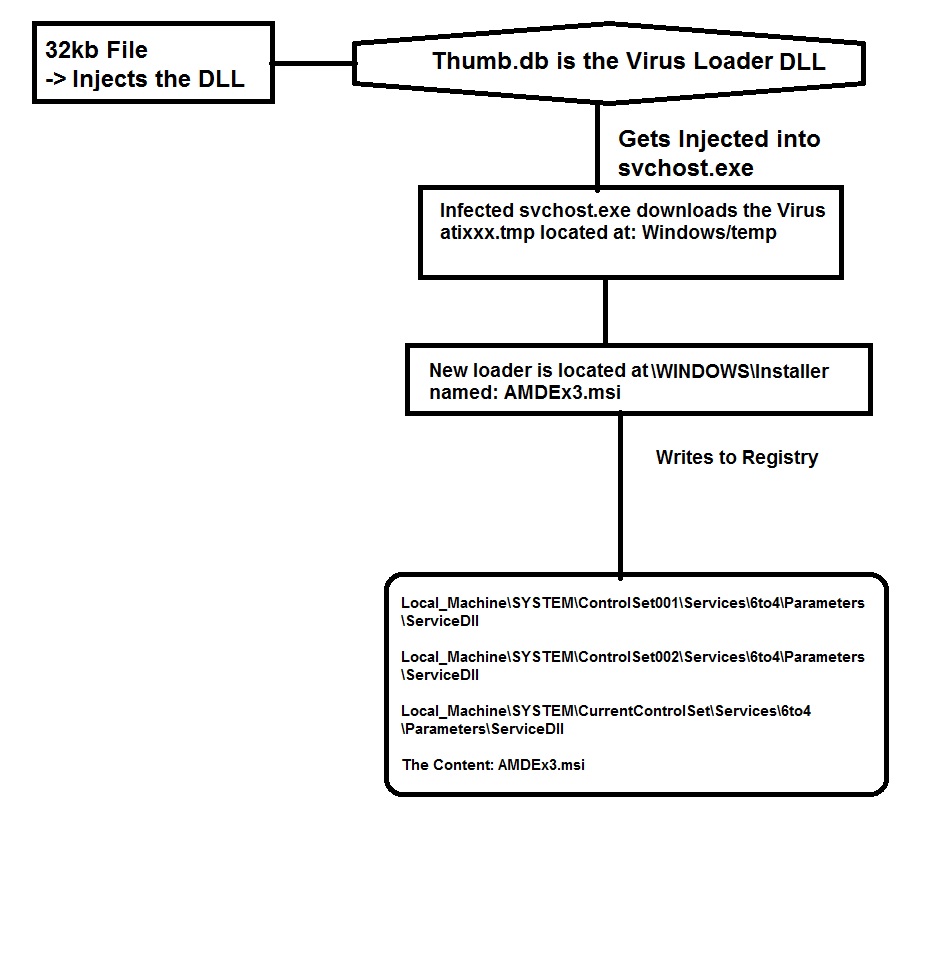
How the Virus Works:
1) If you had click onto the launcher the Executable Vanish and nothing happens.
2) The Virus Injected hisself into the System service (svchost.exe)
3) Now it Downloads the Virus ( Its a Passwordstealer :-( )
4) The Virus is Located at WINDOWS\Temp name atixxx.tmp.
5) If you Reboot it gets loaded by AMDEX2.msi
This was my Infected Registry pathes:
Code: [Select]
Local_Machine\SYSTEM\ControlSet001\Services\6to4\Parameters\ServiceDll AMDEx3.msi
Local_Machine\SYSTEM\ControlSet002\Services\6to4\Parameters\ServiceDll AMDEx3.msi
Local_Machine\SYSTEM\CurrentControlSet\Services\6to4\Parameters\ServiceDll AMDEx3.msi
How to remove manulie FOR PROS!!!:
1) Open cmd.exe
2) enter regedit
3) search for the Registrykeys i provided above.
4) Delete all keys that contain AMDEx...
5) Reboot System.
6) Go to Windows\Temp and Delete atixxx.tmp
7) Go to Windows\Installer and Delete AMDEx....msi
That should remove the Virus
This Tool detects and can remove it:
I found the Tool Malwarebytes. It detects and can remove the Virus. Please folow the Instructions on the Malwarebytes homepage.
Malwarebytes Anti-Malware - CNET Download.com
For all who are intrested on the Virus code, that is what i could recover from it:
[C] Virus >.< - Pastebin.com
[C] Virusv2>.< - Pastebin.com
N/U pastebin
Regards from
Hamburger and from
Crawli ;-)